

How to Integrate Cybersecurity with Your IT and Internal Audit Teams
By Steve Fineberg, Partner, Internal Audit Services, Moss Adams
By Kevin Villanueva, Partner, Cybersecurity Consulting Services, Moss Adams
Original Publish Date: September 7, 2021
IT and internal audit teams share a common goal to protect your organization from risks, but collaboration between teams can sometimes cause friction due to key differences in approach and language.
If you can better understand how these teams interact, and some of the common collaboration challenges they face, your organization can help facilitate a stronger cybersecurity defense.
What Are IT and Internal Audit Teams’ Roles in Cybersecurity?
Many companies augment their cybersecurity efforts with internal audit teams, which evaluate internal controls, regulate risks, and streamline operations.
IT and internal audit teams are part of a larger cybersecurity strategy, with separate responsibilities and focus areas. Regardless of the organization’s size, industry, market, or risk tolerance, successful defense requires coordination and a shared ethos of risk management.
The graphic below shows an example of how these teams fit into a company’s overall security operations.
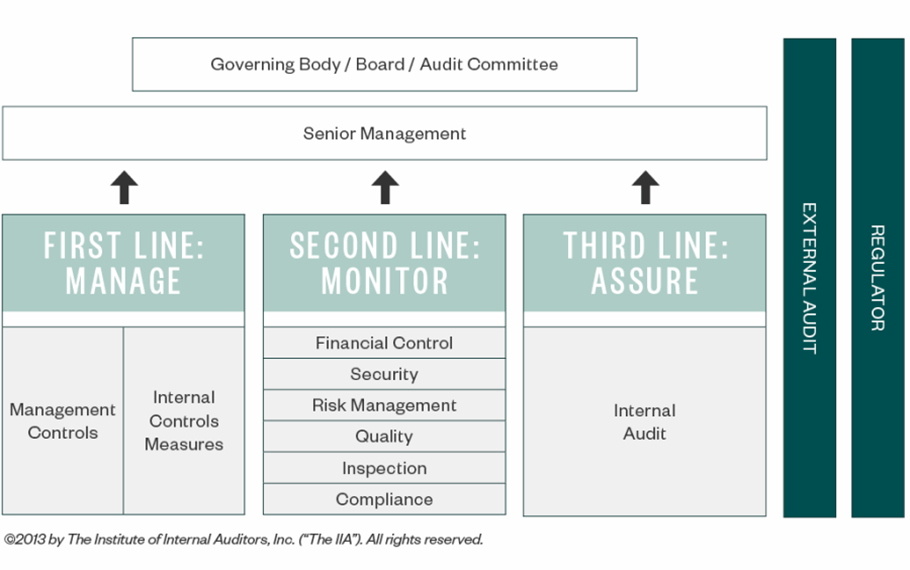
First Line: Manage
The first line of defense involves the front-line process owners assessing activities that create underlying risks.
For the objectives of cybersecurity, the goal is to identify underlying cyberthreats and design and implement controls to address them.
Second Line: Monitor
Once the proper controls are in place, the next step is for senior management to leverage their competence and expertise, monitor these controls, and make sure operations run effectively.
This second line of defense helps address underlying objectives of first line activities and operations. This is especially important in a remote work environment.
Third Line: Assure
In the final line of defense, the audit committee acts as an objective and unbiased resource that should report to the board to avoid influence from the management team. The committee uses independent validation to assess their ability to address cyberthreats appropriately and effectively.
The internal audit team plays the role of both police and advisor, which means internal audits are only effective when there’s trust between IT, the audit team, and other departments across the organization. Collaboration between these teams helps unveil problems - and provides quicker identification and solutions development.
Doing one thorough review as opposed to frequent ineffective reviews helps improve the efficiency of the audit process, and the best way to achieve that is to make sure both groups understand the value of working together.
Having the governance team working with the IT team to share a big picture understanding of the risks as part of due diligence can be hugely beneficial. In the same vein, internal audit teams should have a relationship with the board and work with IT to communicate up to the board.
How Can IT and Internal Audit Teams Improve Their Collaboration?
While IT and internal audit teams share a common goal, their methods and approaches can differ greatly. There are a few steps you can take to help these teams collaborate more effectively:
- Align language
- Increase communication
- Share and understand data goals
Align Language
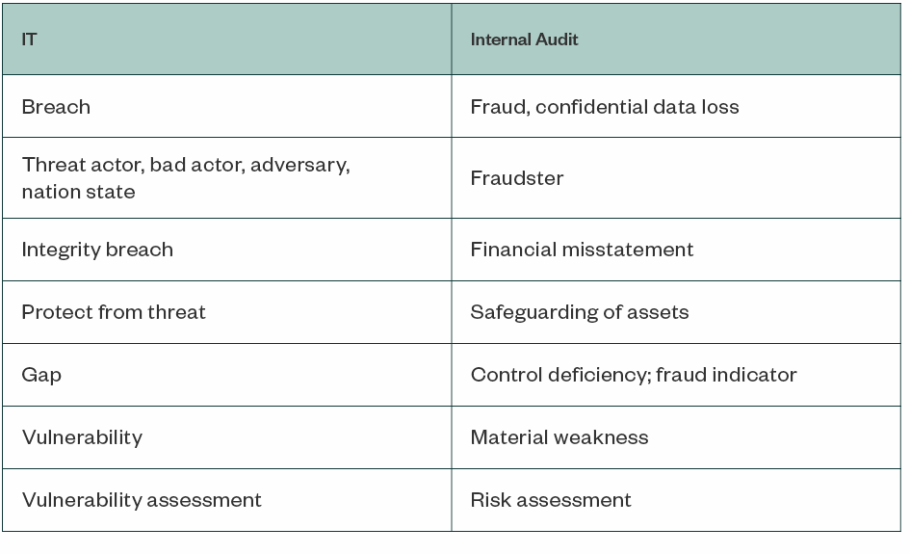
Both IT and internal audit teams have their own languages and terms, which can create barriers to understanding when the two groups work together. Often, auditors who have a technical understanding of IT basics of IT can help reduce confusion.
Here are some examples of how teams may use different terms to refer to the same idea.
Increase Communication
Audit and IT teams frequently compete for the same budget and funding resources using different control frameworks, which means divisions occur naturally, and basic attitudes between each team can be vastly different.
For example, compliance for an IT team is considered a baseline security standard, whereas internal audit teams see it as one of several factors to consider when it comes to security. Cyberthreats often move faster than compliance standards can be written or adjusted to deal with these security issues.
Internal audit teams are often further from an issue in terms of process and time. IT establishes their security standards, and the results needed to be audited and examined after a period of time to search for gaps or breakdowns.
Any issues identified by the internal audit will then be remediated. Internal audit teams could have a broader, more holistic view of the organization that allows them to assist with more cross-functional solutions.
However, in that same time period, other cyberthreats could occur and change; IT needs to respond immediately to address any risk. That’s why it’s important for IT to communicate issues with other teams in a timely manner, so they have the appropriate budget to address solutions.
Due to the independence and objectivity requirements placed on internal audit teams, it can often seem like their role is to police security, although it’s really to improve overall security. Taking these differences into account can help smooth friction between the two teams as they work toward achieving shared goals.
Other ways to improve collaboration include:
- Communicate the importance of audit efficiency to improve the audit and cybersecurity experience
- Prepare and provide the list of reports or system reviews needed ahead of the audit
- Solicit IT leadership’s feedback on high-risk target approaches
- Use audit findings to help drive remediation projects and increase budgets for security
- Create cross-functional committees or communities to foster better communication practices
Share and Understand Data Goals
The ultimate goal is the confidentiality, integrity, and availability of sensitive data. This includes:
- Protecting tangible and intangible assets
- Reducing the possibility of fraud
- Knowing the types and location of data within the enterprise, such as personally identifiable information (PII)
- Creating a systematic approach to improve the effectiveness of risk management, control, and government processes
- Understanding all frameworks used across all areas of compliance, such as COSO or Cobit 5, as well as the framework used by the IT team to assess security, such as NIST 800-53 or 800-171, ISO 27001, or HITRUST CSF
Through increased and transparent collaboration, IT and internal audit teams work toward improving the security and functionality of their organization.
They can design an audit that will allow for the greatest amount of collaboration, so they’re able to prevent, spot, and address cyberthreats as quickly as possible.
We’re Here to Help
For more information about strengthening collaboration between your IT and internal audit teams, contact your Moss Adams professional.
Steve Fineberg has been providing auditing, accounting, and consulting services since 2003. He helps clients streamline their risk compliance efforts through risk assessments, controls evaluations, and operational effectiveness testing. He can be reached at (916) 503-8175 or stephen.fineberg@mossadams.com.
Kevin Villanueva has been in the IT field since 1997. He focuses on IT security assessments, penetration testing, HIPAA compliance audits, and strategic technology planning. He can be reached at (206) 302-6542 or kevin.villanueva@mossadams.com.